Can Blockchain Be Hacked?
Wondering if blockchain can be hacked? In this article, we will answer this question.
How does blockchain dissuade hackers?

Before exploring if blockchain can be hacked in detail, let’s understand how this technology keeps hackers at bay. Blockchain guards against hacking as follows:
1. Digital signature:
Digital signatures protect users as follows:
- Users need to use their digital signatures for transactions, which use public-key/private-key data encryption techniques.
- They can share their public key, however, they must guard the private key.
- This technique uses "Integer factorization" to link public and private keys.
- Hackers can’t extrapolate the private key from the public key since currently, available computing technology will need billions of years to crack it.
2. Decentralization
Decentralization secures blockchain as follows:
- Each node, i.e., a computer in a public blockchain network, hosts the entire transaction data in the network.
- Every one of these nodes effectively acts as a complete ledger of all transactions, therefore, we call it “Distributed Ledger Technology” (DLT). Read “Distributed ledgers definition” for more insights.
- Hackers can't shut the network down by taking over just one or two computers since the other computers will still maintain the network and resist any changes.
3. Transaction validation
No transaction in the blockchain goes through without validation. Public blockchains like Bitcoin validate transactions as follows:

Get a complimentary discovery call and a free ballpark estimate for your project
Trusted by 100x of startups and companies like
- All nodes participate in transaction validation.
- “Crypto miners”, i.e., nodes with specialized hardware and software solve a computing-intensive cryptographic puzzle in a competitive environment. The first miner solving this puzzle can create a new block with new transactions.
- This is a transparent process, and malpractice is possible only if hackers capture the majority of the computing power in the network. That's hard to do in a decentralized network.
- Crypto mining is energy intensive and, these days requires a large investment. Hackers hardly have economic incentives in this environment.
4. Preventing “double-spending”
Cryptocurrencies are mathematical money. “Double-spending” is a risk here, which involves spending the same cryptocurrency more than once. Hackers can change the destination address of a cryptocurrency transaction and cause double-spending. Public blockchains prevent this as follows:
- Each block has the cryptographic hash of the earlier block.
- Hackers trying to cause double-spending need to change the transaction data in a block. When they do so, the cryptographic hash changes, therefore, they need to change the next block to incorporate the new hash. As soon as they do that, they must change the subsequent block, and this must go on till the last block!
- In a transparent network, everyone will soon notice such activities.
- Moreover, hackers must find a small enough hash, i.e., with enough-leading zeroes, before anyone else accepts the new hash value. That’s very hard to do.
Blockchain and hacking: Public vs private blockchains
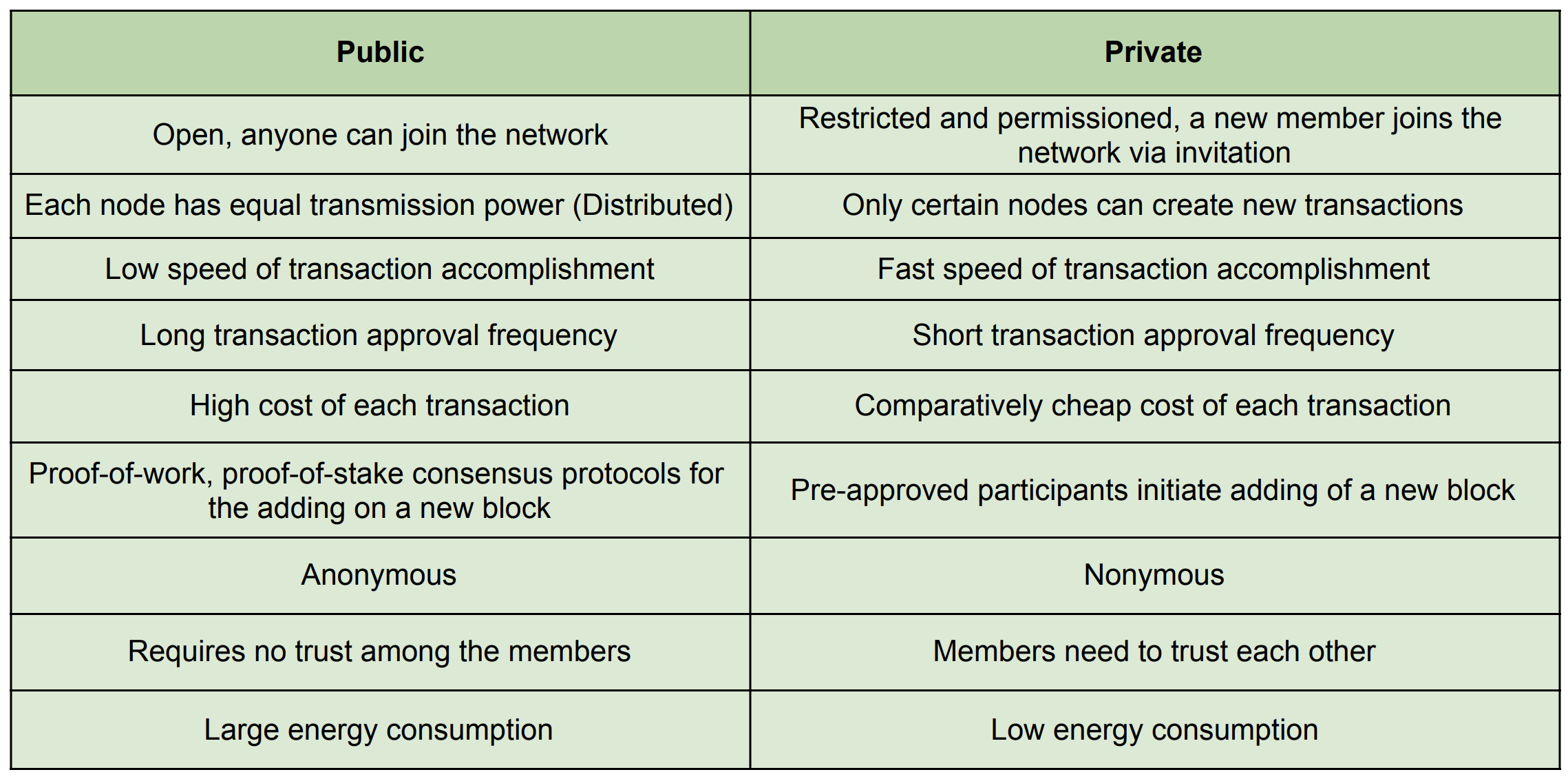
Most discussions around hacking a blockchain revolve around public blockchain networks. Private blockchain networks hardly figure in these discussions since these networks are fundamentally different. The reasons are as follows:
- Public blockchains like Bitcoin network and Ethereum are open to all, including anonymous and pseudonymous users. On the other hand, enterprises use private blockchains, and they only allow trusted entities to join these networks.
- Transaction records on a public blockchain are transparent, and every user can view them. Private blockchains differ here since they provide separate security measures for sensitive data including implementing access control.
Read “Public vs private (permissioned) blockchain comparison” for more information.
Take, for e.g., Hyperledger Fabric, a popular enterprise blockchain framework. It offers the following security features:
- Organizations can implement the framework in their on-premises secure infrastructure. Alternatively, they can use highly secure “Blockchain as a Service” (BaaS) offerings like the IBM Blockchain Platform.
- Hyperledger Fabric, or Fabric as it’s commonly called, offers access control.
- Fabric has channel technology for sensitive data, which uses data partitioning for added security.
- There is also an additional “Hardware Security Model” (HSM) for digital signatures.
Read “Pros and cons of Hyperledger Fabric for blockchain networks” to learn more about the security features of Fabric.
In this article, I focus on public blockchains while analyzing whether blockchains can indeed be hacked.
Crypto exchange hacks: Not blockchain hacks
Newcomers in the blockchain/crypto space often confuse crypto exchange hacks with blockchain hacks, however, these are quite different. The following facts help us in understanding why:
- Different public blockchains use different technology stacks. They are not interoperable, therefore, you can’t transact on the Ethereum network using Bitcoins.
- Against this backdrop, crypto exchanges emerged to facilitate crypto trading for users. For e.g., you can buy Ether in exchange for your Bitcoin in such exchanges. Read “What are centralized cryptocurrency exchanges?” to learn about them.
- Popular crypto exchanges are mostly centralized 3rd party services. While they make crypto trading easier, their central servers are vulnerable to hackers just like any other central server elsewhere!
- When hackers attack such crypto exchanges, which they often do, it’s not an attack on a blockchain network. It’s simply an attack on a central server.
Can blockchain be hacked, and how?
I will now take you through the key question of whether blockchain can be hacked, and how this could be possible. There are the following possibilities in this regard:
1. “51% attack”
This is one of the highly-discussed modes of attacking a blockchain network. A 51% attack would work as follows:
- Assume a public blockchain network has quite a few nodes, and it uses the “Proof of Work” (POW) consensus algorithm.
- Each node uses specialized hardware and software for crypto-mining, which is the transaction validation method for the POW algorithm.
- The network is decentralized, and users operating nodes are not in any cartel. They operate according to the established rules of the network and validate transactions.
- None of the node operators can overpower the computing power of other nodes combined, therefore, none can get any undue advantage.
- Now, suppose hackers procure enough computing power to control more than half of the total computing power in this network.
- They now have a higher hash rate than the other nodes, which increases their mining success rate. Read about the hash rate in "What is the hash rate?”.
- These hackers can now solve the cryptographic puzzle required in POW faster than the other nodes.
- They can then manipulate transaction history and cause double spending.
Read more about this in this article on the “51% attack”.
What are the chances of hackers successfully pulling off a 51% attack? Let’s consider the following aspects:
- Public blockchain networks like Bitcoin and Ethereum have many nodes. With their popularity increasing even more nodes are joining these networks.
- The higher the number of nodes in a blockchain network, the higher the cumulative computing power in the network.
- This makes it harder for hackers to control 51% of the total network's computing power in such networks. Essentially, a higher number of nodes add more security against 51% of attacks.
- However, less popular blockchains have a lesser number of nodes, therefore, hackers can launch 51% of attacks more easily. In 2018, hackers targeted a few relatively new cryptocurrency networks with a lower number of nodes. Verge, Monacoin, and Bitcoin Gold had fallen victim to these 51% attacks, as this “MIT Technology Review” report shows.
Let's also understand how market economics provides natural protection against 51% attacks:
1,200 top developers
us since 2016
- A cryptocurrency blockchain with limited popularity would naturally mean that the coin has a low price in the crypto market. Hackers staging a 51% attack might gain coins, however, their profit will be low.
- On the contrary, staging a 51% attack on the blockchain of a popular cryptocurrency like Bitcoin will require very high computing power. The investment, including the electricity bill, will be very high. The network is transparent. Users will soon know if hackers stage a 51% attack, and the Bitcoin price will plummet. Once again, hackers will be left with almost no profit.
Read about this economic aspect in “Bitcoin’s attack vectors: 51% attacks”.
2. Exploiting bugs in the blockchain protocol code
Blockchain uses modern cryptography, which is founded on complex mathematics and programming. Complex programs can have bugs, and hackers can exploit them.
An example was a 2010 incident of hacking the Bitcoin protocol, which played out as follows:
- A piece of code in the Bitcoin protocol checked Bitcoin transactions.
- This piece of code wouldn't work if the output was too large, causing an overflow when summed up.
- An unknown hacker took advantage of this bug and created 184.467 billion Bitcoins, whereas the maximum supply of Bitcoins is predefined as 21 million!
- Satoshi Nakamoto, the pseudonymous creator of Bitcoin, and Gavin Andersen, another Bitcoin developer worked together and fixed the bug within a few hours.
- They forked the Bitcoin blockchain to create a good chain, monitored the chain created by the hacker, and persuaded the other miners to avoid it.
Read more about this hack in “Bitcoin’s biggest hack in history: 184.4 billion Bitcoin from thin air; Satoshi hard forks saves Bitcoin”.
The likelihood and impact of such attacks are unpredictable, due to the following reasons:
- Hackers must have highly advanced knowledge to identify and exploit bugs like the above in blockchain protocol programs.
- Blockchain developers that created the network also need robust programming skills to prevent such bugs and to recover from such attacks quickly enough.
3. Exploiting bugs in a poorly coded smart contract
This is essentially exploiting bugs in programs running on a blockchain network, rather than hacking the network itself. This kind of hacking incident can have a serious impact.
Smart contracts are programs that run on blockchain networks like Ethereum, NEO, etc. They have the following characteristics:
- Smart contracts are open-source pieces of code that transfer cryptographic assets based on predefined conditions.
- They are stored in a blockchain, therefore, one can't modify them after deploying them.
- They execute automatically, and the execution results are also recorded in a blockchain. This means that their execution is irreversible.
Read more about smart contracts in “How to deploy a smart contract on Ethereum?”.
Hackers can exploit bugs in smart contracts and make off with crypto tokens. An example was the 2016 Ethereum “Decentralized Autonomous Organization” (DAO) hack, which panned out as follows:
- The Ethereum community set up an investment fund in 2016 to manage improvement proposals, and a DAO to govern it.
- They used smart contracts for managing the DAO.
- While the Ethereum network protocol program was fine, the smart contract running on this network had a bug. One could keep requesting money from the DAO account, while the system didn’t record that the money is already withdrawn.
- Hackers used this bug and made off with $60 million worth of Ether.
- After much deliberations and controversies, the Ethereum community executed a hard fork. Today’s Ethereum network is the result of this hard fork, however, some community members continued with the old chain. The old chain is called “Ethereum Classic”.
Read “Understanding the DAO attack” for more information about how blockchain can be hacked through this attack.
More and more developers are creating smart contracts, and some of them will have bugs. This potentially raises the likelihood of such attacks. Hackers need the required skills to exploit such bugs.
At the same time, blockchain programmers need sufficient expertise to write new smart contracts that can help recover from such attacks.
4. Lunching Sybil attacks
A Sybil attack on a blockchain network involves one malicious user owning a large number of nodes. The user can then swamp the network with fake transactions, or prevent validation of good transactions.
The probability and impact of such attacks vary depending on the design of the blockchain, as follows:
- Blockchain networks using the POW algorithm will require each node to spend significant computing power. These nodes also run up high electricity bills, therefore, the incentives are less.
- On the other hand, blockchain networks using the “Proof of Stake” (PoS) algorithm will require transaction validators to stake their coins. This can reduce the incentives to launch such attacks.
Read “What’s a Sybil attack & how do blockchains mitigate them?” to learn more about such attacks.
5. Staging “Direct Denial of Service” (DDoS) attacks
A "Direct Denial of Service" (DDoS) attack involves sending an exceptionally large volume of traffic to a server. In the case of a blockchain network, this amounts to sending too many spam transactions.
DDoS attacks on blockchain networks are common since many hackers and malicious organizations sell such attacks. However, these attacks have limited impact, due to the following reasons:
- Most blockchain networks included best practices to manage situations arising from DDoS attacks.
- Miners in cryptocurrency networks like Bitcoin have sufficient experience with these attacks. They can easily identify such sudden bursts of spam transactions, and prevent them from being validated. As a result, no funds are stolen, however, the network activities may be halted for some time.
Read, “Yes, the blockchain can be hacked” for more insights into how blockchain can be hacked through DDoS attacks.
Wondering how to prevent hacking of your blockchain network?
If you are planning to start a strategic blockchain project involving a new network, you need to prevent hackers from attacking it. That’s not an easy task.
You need software architects with sufficient blockchain expertise to design such a network and undertake development.
Consider engaging a reputed software development company for such projects. Read "What to plan for when undertaking blockchain software development?” before you engage a partner.
DevTeam.Space can help you here with its experienced community of blockchain developers. Write to us your initial blockchain application development and security project details via this quick form. One of our technical managers will get back to you for further discussion on your product team, development plan, etc.
Frequently Asked Questions on Can Blockchain be Hacked?
Blockchain was designed to allow data to be shared in such a way that it would be immutable. While some experts have claimed to have been able to overcome security features such as the 51% rule, blockchain is still a far more secure alternative to traditional centralized databases.
Blockchain technology uses cryptography. It requires each transaction to be authorized by a private key and also requires 51% of the network to validate any transactional change.
Blockchain bloat means more and more computational power and storage are required as more data is added. Blockchain is not anywhere near an energy-efficient and centralized storage solution. Private keys, if lost, are not replaceable.